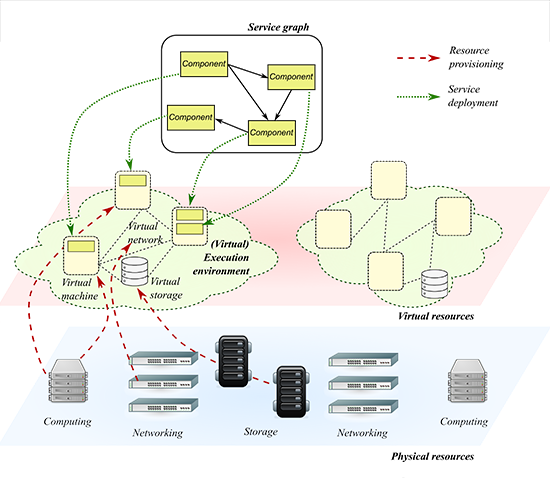
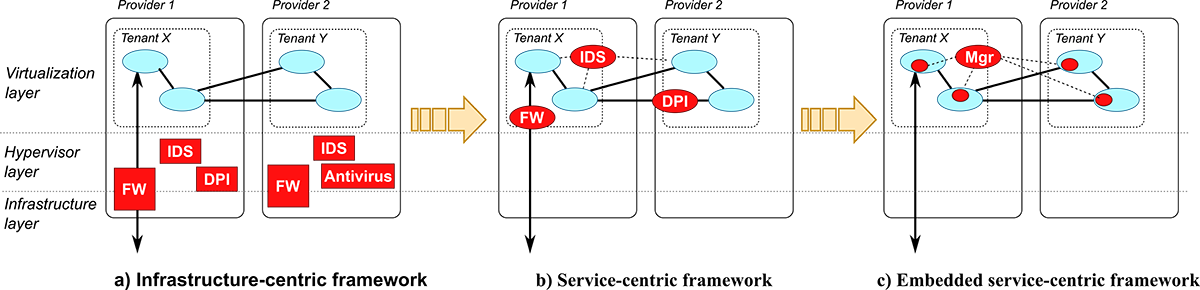
The Infrastructure-as-a-Service (IaaS) model is a very effective and agile paradigm that provides computing, storage, and networking resources corresponding to physical instances (servers, switches, disk arrays, network links). Although de-coupling software from the underlying infrastructure brings immediate benefits in terms of elasticity, portability, automation and resiliency, the intermediate hypervisor tier also raises new security concerns about the mutual trustworthiness between those two layers and the potential threats in the virtualization substrate. The objective impossibility to apply the legacy security perimeter model to emerging software architectures has boosted an increasing interest in the development of security and privacy solutions for the new paradigms. This effort has resulted in commercial and open-source security appliances for the cloud, including distributed firewalls, antivirus, intrusion detection systems, and identity/privacy management, often implemented in the hypervisor layer (infrastructure-centric cyber-security framework).
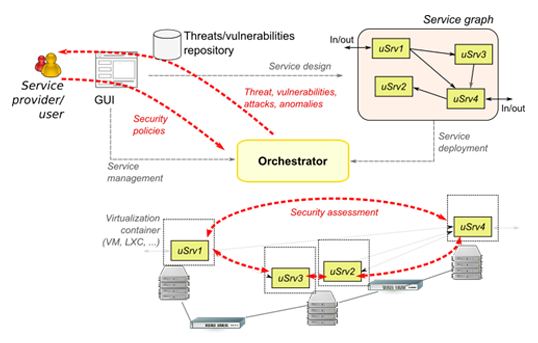
Virtual security functions can be easily “plugged” into service graphs, leveraging the large correspondence with physical infrastructures that is present in this case (service-centric cyber-security framework). However, application to other cloud models is not straightforward, especially when some software components are shared among multiple tenants (i.e., Service-as-a-Service), they should run on resource-constrained devices (i.e., the fog or IoT), or the service topology changes over time (e.g., for scaling, discovery of new components, failures). In addition, given the lack of standard APIs and control interfaces, data collection, harmonization, and correlation may be very difficult.
The distinctive aspect of the ASTRID approach is that no explicit additional instances of security appliances are added and deployed in the execution environment, which is the typical approach of some recent proposals in this field. The main concept is the disaggregation of cyber-security appliances into business logic (i.e., detection algorithms) and data plane (i.e., monitoring and inspection tasks), mediated by orchestration logic and proper security models. Instead of overloading the execution environment with complex and sophisticated threat detection capabilities, efficient processing capabilities are embedded in the execution environment that create events and knowledge; algorithms for detection of threats and vulnerabilities are moved upwards and process such data in a coordinated way for the whole execution environment (embedded service-centric cyber-security framework).
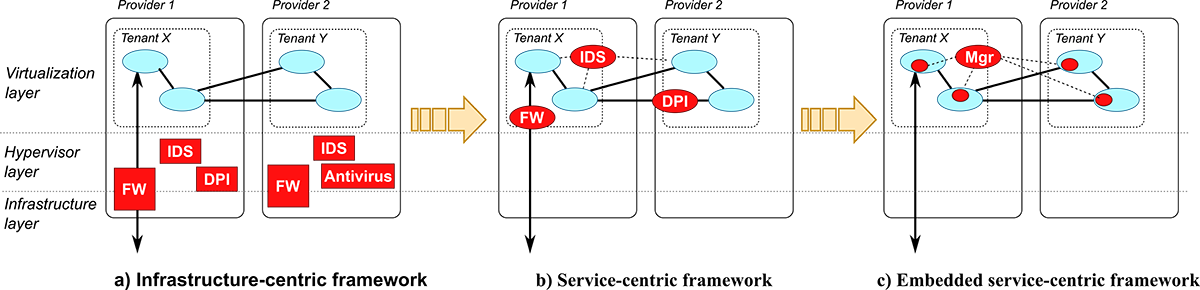
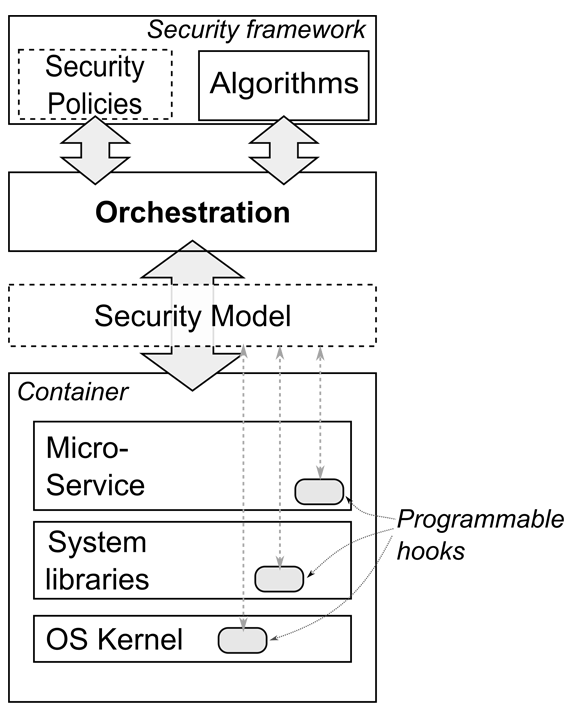
The vision of ASTRID is therefore a transition from infrastructure-centric to embedded service-centric cyber-security for virtualised applications. To achieve this objective, ASTRID envisions a multi-tier architecture, where multiple programmable hooks are present in the virtualisation container (in the OS kernel, in system libraries, and in the virtual function code), to monitor and inspect what happens inside. An intermediate layer decouples programmable hooks from orchestration (the Security Model), which gathers data and feeds algorithms for detection of threats, anomalies, vulnerabilities, attacks. This approach split the main detection logic from monitoring and inspection.
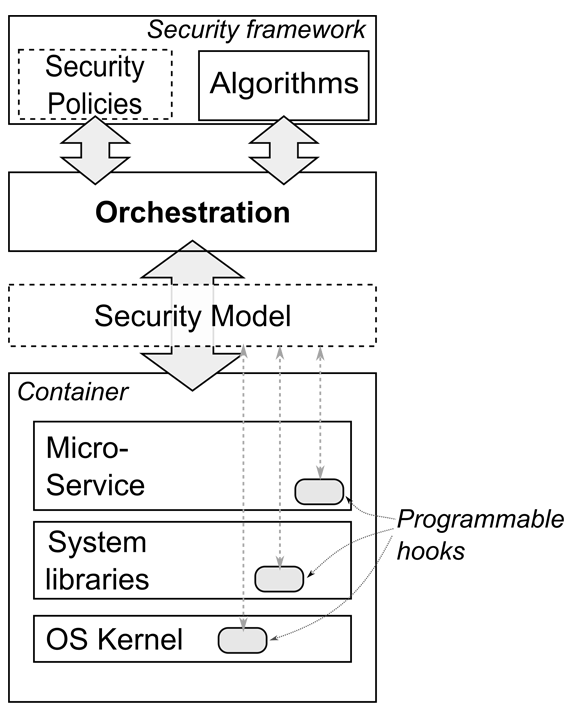
Programmable hooks include logging and event reporting capability developed by programmers into their software, as well as monitoring frameworks built in the kernel and system libraries that inspect network traffic and system calls.
The Security Model uses specific semantics to describe what security functions the component provides, e.g., logging, event reporting, filtering, deep packet inspection, system call interception. Through the Security Model, Orchestration knows what kinds of operations can be carried out on each component, collect data and measurements, and feed the detection logic that analyse and correlated information at graph level to detect threats.
Decoupling the detection logic from inspection and monitoring operation brings the following advantages:
- shift complex processing tasks to high-performance dedicated infrastructures (e.g., cloud installations with big data paradigms – Hadoop or Spark), while relying on pervasive and capillary lightweight operations for monitoring and inspection tasks (hence enabling re-usage of the same information for multiple purposes). This approach represents a disruptive evolution from deployment of security appliances in service graphs;
- facilitate the integration with a set of continuous risk-assessment and management mechanisms able to evaluate in real-time the existing risks and propose the appropriate mitigation actions, along with a set of data mining, analysis and threat intelligence mechanisms for getting advanced insights with regards to security aspects and support application of analytics-driven security mechanisms;
- the “in-environment” embedding of security and the ability to deploy multiple networks in parallel, give the ability to run in parallel a “honey-pot” network which is able in real time to detect the types of attacks on the system and to add new signature attacks to the orchestration system;
- reduced overhead on graph execution and attack surface, since most of the detection logic typically integrated in security instances is shifted outside the service graph.